For a long time, compliance was something teams braced for.
A big deadline appeared, roadmaps shifted, developers got pulled into urgent remediation, QA teams absorbed the pressure, and leadership approved extra spending. Then, once the push was over, everyone tried to return to normal product delivery.
That model is under strain now.
The compliance environment around certified health IT is moving more often, across more layers, and with more operational consequences than before. HTI-1 expanded certification and transparency expectations. USCDI continues on an annual basis. Standards updates, implementation dates, reporting timelines, and maintenance obligations now shape planning throughout the year rather than around one isolated push.
That shift matters because the systems affected by these requirements are not niche. ASTP/ONC says ONC-certified health IT supports the care delivered by more than 96% of hospitals and 78% of office-based physicians in the United States. When regulation and standards change in an environment with that kind of footprint, compliance stops behaving like a side project. It becomes part of how product, engineering, QA, and release teams operate.
What project-based compliance usually looks like
- Sudden escalation before deadlines
- Engineers pulled off roadmap work
- QA is overloaded late in the cycle
- Documentation rushed at the end
- Higher remediation costs
- Customer-facing priorities pushed back
The real issue is whether they can keep absorbing that kind of disruption without damaging roadmap confidence, engineering focus, release quality, and cost predictability.
Compliance Deadlines No Longer Occur Every Few Years — They Are Constant
The older planning model assumed longer periods of stability between major compliance pushes.
That assumption is harder to defend now.
The pressure no longer arrives through one large event followed by a long reset. It shows up through smaller but more frequent changes that affect planning, testing, data readiness, and product maintenance across the year.
What keeps moving now
- USCDI evolves annually
- Implementation dates continue to reshape planning
- Standards bulletins keep advancing the data landscape
- Certification maintenance requires ongoing attention
- Reporting-related obligations require earlier readiness
The current dates alone make the point. Draft USCDI v7 was released on January 29, 2026. ASTP/ONC says it includes 29 proposed data elements and one significantly revised data element, for 30 overall proposed additions. An ASTP/ONC overview presentation also notes that Draft USCDI v7 includes 156 data elements in total.
That is only part of the picture. HTI-1 moved certification to USCDI v3 as the required baseline, effective January 1, 2026. HTI-1 also created the Insights Condition, with applicable data collection beginning in January 2026 and required reporting for certain measures beginning July 1, 2027.
This is the planning problem.
Teams still treat compliance like a periodic event, while the environment has shifted toward continuous movement.
By the time many organizations react, the timeline already feels compressed.
Roadmaps Break When Compliance Is Treated Like a Project
Compliance creates the most damage when it is entered late and collides with work that is already committed.
It rarely stays contained in one team. A standards update may require changes in data models. An API expectation may expose inconsistent behavior across modules. A transparency or reporting requirement may reveal gaps in instrumentation, evidence trails, or documentation discipline. What starts as “compliance work” quickly reaches product planning, architecture, testing windows, support readiness, and release coordination.
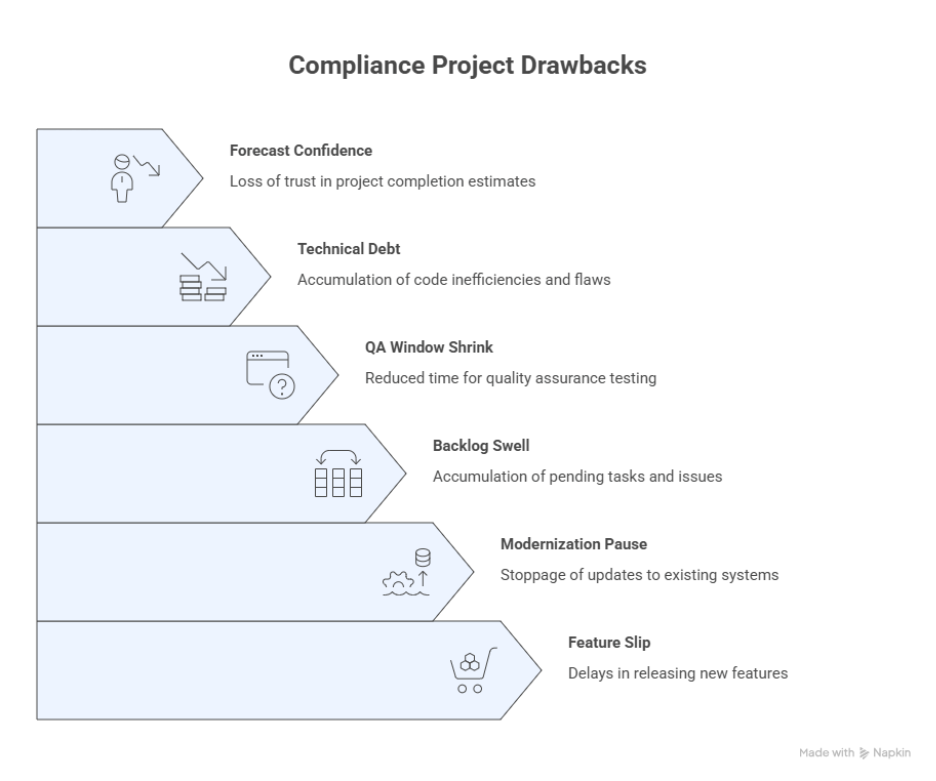
Where the damage shows up
- Feature releases slip
- Modernization work pauses
- Backlogs swell
- QA windows shrink
- Technical debt gets exposed at the worst time
- Leadership loses forecast confidence
This is one reason the disruption feels so severe. The issue is timing. Compliance often enters after roadmap commitments have already been made, which turns it into forced reprioritization rather than planned execution.
There is also a broader engineering cost behind that disruption. Stripe’s Developer Coefficient report found that developers estimated spending 13.5 hours per week on maintenance work such as debugging, refactoring, and modifying bad code, while companies reported an average of 17.3 hours per week spent addressing technical debt. When late compliance work lands on top of existing engineering drag, the disruption becomes harder to contain cleanly. (Stripe Developer Coefficient PDF)
Last-Minute Compliance Is the Most Expensive Way to Do It
Reactive compliance creates the same work under worse conditions.
When teams wait too long, they still have to perform the same analysis, engineering changes, validation, documentation, and readiness work. The difference is that they do it inside a narrower window with more pressure and fewer clean options.
Why costs rise in a reactive model
- Compressed timelines
- Context switching across teams
- Duplicate or rushed testing
- Emergency SME involvement
- Release coordination overhead
- Less time for architecture cleanup
- More rework when issues are discovered late
That combination drives cost in ways leadership often feels before it can measure precisely. Engineering time becomes fragmented. QA loses stable validation cycles. Product teams have less room to sequence work properly. Program coordination becomes heavier because more dependencies are moving at once.
McKinsey has emphasized that software productivity depends on the broader operating system around developers, including workflow quality, collaboration, environment, and organizational friction. That matters here because late compliance worsens those conditions at the same time. (McKinsey)
Reactive compliance compresses the same work into a shorter, more expensive, and less predictable window.
If compliance keeps showing up as a budget spike, the operating model deserves a closer look.
See Where Compliance Is Creating Avoidable Risk
When roadmap pressure, documentation gaps, API readiness issues, and standards changes keep surfacing late, the problem is usually bigger than execution.
It usually points to a compliance model that is too reactive.
A structured review can show where that pressure is building and what should move into a continuous workstream before the next major deadline arrives.
Modern Compliance Requires Continuous Monitoring
Modern compliance depends on visibility.
Teams need to know what is changing, where risk is surfacing, and how releases affect compliance-sensitive workflows before that pressure becomes urgent. Without that visibility, readiness becomes guesswork, and teams end up learning too much too late.
What teams need visibility into
- API behavior and error patterns
- Data mapping consistency
- Logging and evidence trails
- Documentation accuracy
- Release-level compliance impact
- Readiness for testing, review, and reporting
This is one of the clearest signals that the old project model no longer fits. Monitoring cannot be bolted on at the end. It has to exist across the year if teams want earlier warning, cleaner evidence, and better release discipline.
The federal direction supports that view. HTI-1 created the Insights Condition within the ONC Health IT Certification Program. The published key dates show applicable data collection began in January 2026, with required reporting for certain measures beginning July 1, 2027. Even where some obligations have been phased or moderated over time, the operating message remains the same: better instrumentation, better evidence readiness, and better transparency matter more now than they did in older compliance cycles.
Compliance-as-a-Service Helps You Scale With Confidence
Growth changes the shape of compliance.
As platforms expand into new specialties, new customer segments, new modules, new geographies, and new regulatory milestones, the number of places where compliance gaps can appear grows with them. A model that feels manageable at one stage of growth often becomes fragile once the product footprint starts widening.
Complexity rises when teams add
- New specialties
- New customer segments
- New modules
- New markets and geographies
- New interoperability and regulatory milestones
- New partner and platform integrations
This is where a continuous compliance model becomes far more valuable than a project-based one. It gives teams a compliance engine that scales with the business instead of forcing them to rebuild readiness from scratch every time the platform grows.
What CaaS helps protect as the platform scales
- Every release is easier to keep certification-safe
- Every module is easier to keep aligned with evolving USCDI expectations
- Every workflow is easier to review against audit and oversight requirements
- Every API is easier to manage against predictability and interoperability expectations
That matters even more in the current environment. Draft USCDI v7, released on January 29, 2026, includes 30 overall proposed additions, showing that the standards landscape is still expanding. Growth no longer happens in a stable compliance environment. It happens in one that continues to move.
As the business grows, compliance has to grow with it.
That is one of the clearest reasons to run it as a service instead of an occasional project.
The Future of Compliance Is Continuous
The direction is becoming harder to ignore.
Compliance is moving away from episodic inspection and toward a more continuous model of oversight, evidence, standards alignment, and operational readiness. Teams may still experience major deadlines, but the work that supports those deadlines now stretches across the year.
What this era increasingly demands
- Continuous FHIR testing and API readiness
- Continuous visibility into the algorithm and decision-support transparency
- Continuous USCDI evolution planning
- Continuous maintenance of DSI-related updates and documentation
- Continuous readiness for real-world testing and reporting expectations
That does not mean every requirement is active in exactly the same way today. Some timelines are phased, and some obligations continue to evolve. But the larger operating pattern is already visible. HTI-1 introduced broader certification and transparency changes, USCDI continues on an annual update cycle, and HTI-1’s Insights timelines already require earlier data collection and planning than many teams were used to in older compliance models.
What the next few years reward
- Stronger observability
- Better release discipline
- Cleaner evidence readiness
- Earlier standards planning
- Fewer compliance fire drills
This is why compliance works better as a service.
The environment itself has become continuous.
Conclusion
The organizations adapting best are the ones treating compliance as a standing operating function rather than a recurring disruption.
A continuous model does more than help teams stay ready for the next deadline. It helps reduce cost, reduce risk, and protect roadmap velocity while keeping the organization aligned with evolving expectations across the year.
That is the real shift.
Compliance’s nature is to behave like a continuous operational responsibility tied to standards, APIs, documentation, testing, transparency, and release discipline.
Compliance works better when it is treated as a service.
For teams trying to stay ready without repeatedly derailing delivery, that is the smarter, safer, and more scalable way forward.
For organizations evaluating how ongoing regulatory change is reshaping compliance planning, our Healthcare Compliance Services page offers a broader view of how continuous support can reduce disruption and improve readiness across the year.
If your team is still handling compliance through large, disruptive pushes, it may be time to review the model itself. To explore how a more continuous compliance approach could support your product, roadmap, and readiness goals, contact us at info@nalashaa.com
Latest posts by Priti Prabha (see all)
- Why Compliance Should Be a Service — Not a Project - March 13, 2026